Introducing automated risks and issues from risk assessment results
Dr. Heather Buker
Created: February 3, 2022|Last Updated: April 10, 2024
Platform
Turn-key GRC for CISOs, InfoSec leaders & security teams.
Deployment
Flexibly deploy 6clicks across teams, jurisdictions, programs & organizations.
Artificial Intelligence
Powered by the only AI engine purpose-built for cyber & privacy GRC.
By Objective
Run your cyber & privacy GRC programs end-to-end on one platform.
By Requirement
Drive compliance with the most in-demand frameworks and regulations.
By Industry
Integrated capability and content that aligns with your industry.
Customers
Make the most out of your 6clicks investment. Explore valuable resources to drive business outcomes and achieve success faster.
Customer Resources
Customer Success
Advisor & MSP Program
Resources
Company

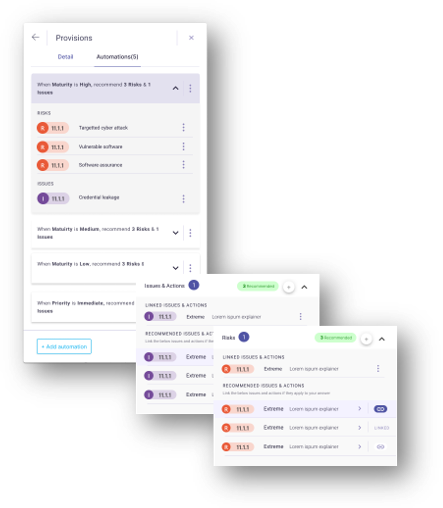
At 6clicks, our relentless pursuit is to streamline processes and enhance efficiency through meticulous automation. Our latest advancement in process automation for audits and risk assessments, unveiled just before the 2021 holidays, exemplifies this commitment.
Check it out:
Curious about learning more? Check out our wealth of content in our 6clicks Knowledge Base below.
Automated Risks and Risk Treatment Plans
Automated Issues and Issue Actions