Digital transformation is a process that involves integrating digital technologies into all aspects of a business to improve its operations and satisfy customer needs. That shift has allowed enterprises to use emerging tech to become more competitive and agile, transforming how they collect, analyze, and store data from different sources, such as cloud computing, the Internet of Things (IoT), and artificial intelligence (AI).
However, that transformation has also made enterprises more susceptible to data security risks like breaches. For example, hackers increasingly target organizations to steal sensitive data such as personal and financial information and trade secrets, resulting in legal liabilities, financial losses, and reputational damage.
Organizations must proactively ensure their data stays compliant and secure and protect its integrity.
But how can organizations ensure data security and privacy?
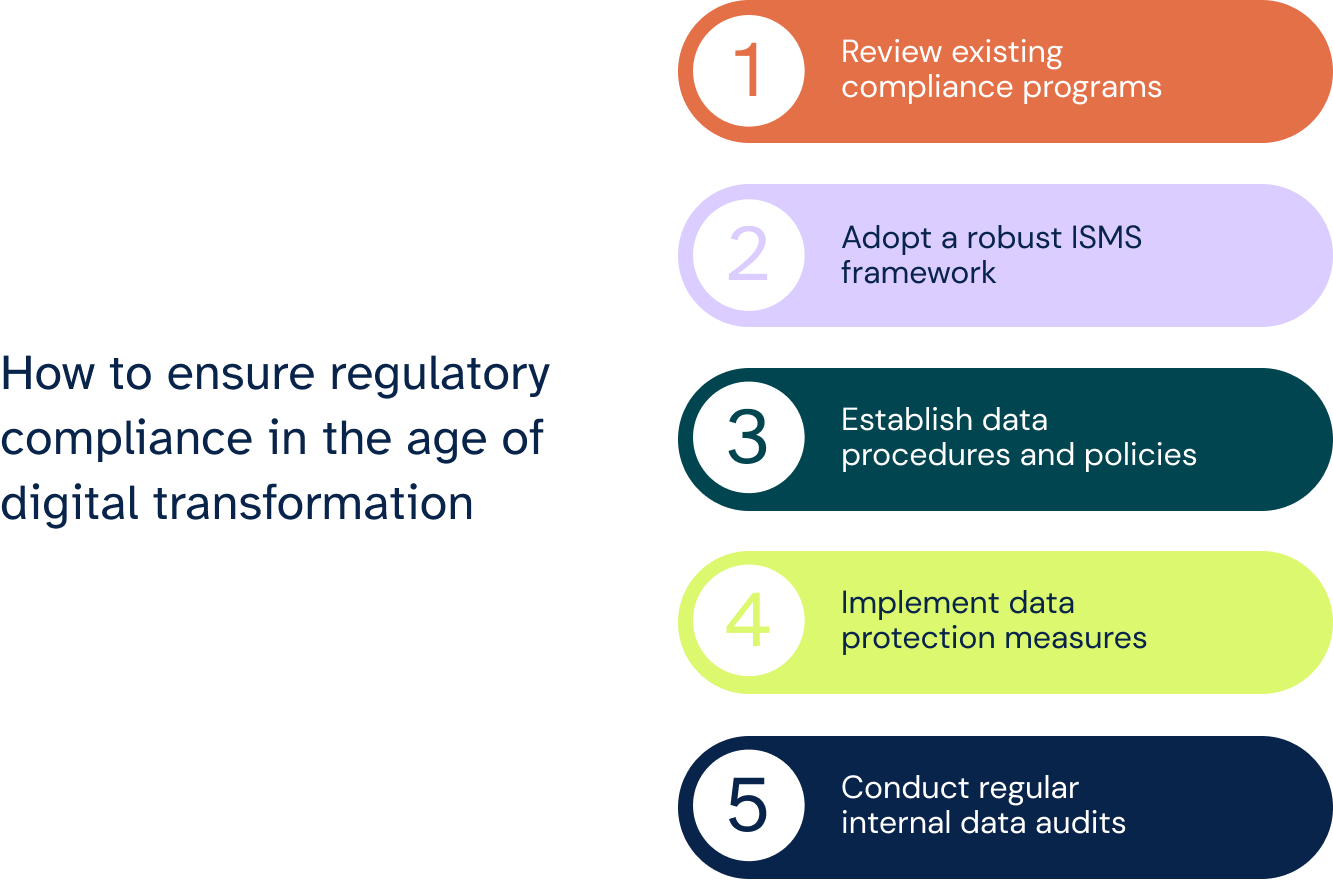
Review existing compliance programs.
Evaluating your existing compliance programs also helps uncover potential gaps and vulnerabilities. For example, a legacy program focused on paper records might not adequately address cloud storage. During your review, examine data governance policies, access controls, security protocols, and breach response procedures.
Once you've identified gaps, you can tailor your existing programs to accommodate the changes caused by integrating digital technologies. That may involve incorporating new data protection technologies, updating policies to reflect best practices for cloud environments, or establishing secure data analysis and usage processes. Building upon existing frameworks can be a cost-effective and efficient way to achieve compliance.
Reviewing your existing programs also allows you to prioritize areas of highest risk, focus on the data types most vulnerable to misuse or breach, and ensure your compliance efforts are most robust in those areas.
Now that we discussed the importance of reviewing existing compliance programs, let’s dive into how it lays the foundation that shapes ISMS in the next section.
Adopt a robust ISMS framework.
With data volumes increasing and regulations progressing, an Information Security Management System (ISMS) becomes crucial in ensuring regulatory compliance and protecting an organization's valuable assets.
Here are a few reasons why ISMS is crucial:
- ISMS frameworks, like ISO 27001, provide a structured approach for managing information security risks through policies, controls, and best practices. They help organizations consistently identify, assess, and mitigate confidentiality, integrity, and availability risks across the entire organization.
- Other ISMS frameworks, like NIST CSF, are designed to be adaptable to various regulations and industries, allowing organizations to demonstrate compliance with many laws and regulations by implementing just the ISMS.
- ISMS frameworks emphasize continuous improvement by having organizations regularly review and update controls to address evolving threats. They keep an organization's security measures current and effective.
Implementing an ISMS gives organizations a standardized framework for managing information security risks and maintaining regulatory compliance, empowering them to operate confidently while protecting their valuable data by providing a structured framework for managing risks, ensuring compliance, and fostering a security culture.
However, its effectiveness depends on its proper implementation and maintenance. Investing in qualified personnel, training, and ongoing assessments is crucial to ensuring its success and maximizing its benefits.
In the previous section, we saw that ISMS lays the foundation for risk identification and assessment, control selection and implementation, and continuous improvement.
Now, we will discuss how data procedures and policies translate ISMS into action.
Establish data procedures and policies.
Enterprises must also establish and maintain data procedures and policies to comply with changing regulations. It defines the rules, responsibilities, and best practices for handling every aspect of your data, from collection to storage, access, and disposal.
Developing data policies and procedures often involves stakeholders across teams to ensure they understand their role in data compliance, fostering a culture of data awareness and an environment where compliance becomes second nature.
Establishing data procedures and policies is inseparable from implementing data protection measures. Together, they work to ensure the effective safeguarding of your data. Learn how in the next section.
Implement data protection measures.
Implementing robust data protection measures can also help overcome the risks associated with digital transformation and ensure regulatory compliance.
One good measure is implementing data governance and management. Data governance sets the principles, policies, and procedures for managing data. It also defines how data is classified, protected, accessed, used, and disposed of.
On the other hand, data management focuses on practically implementing data governance principles. It also involves the tools, technologies, and processes used to collect, store, organize, analyze, and use data.
Here are common data governance and management practices you can implement:
- Implementing a comprehensive data mapping exercise to identify all sensitive data types and their location. That educates employees to classify data based on sensitivity and apply appropriate protection measures accordingly.
- Gathering and retaining only the data used for business purposes, making regular reviews and deletions of unnecessary data pivotal in minimizing potential risks.
- Establishing clear data retention policies that comply with changing regulations and meet business goals to ensure data is securely deleted or anonymized when its retention period expires.
Your organization can also follow the privacy-by-design approach to developing systems, technologies, and business practices with data privacy in mind from the beginning. Instead of adding privacy features as an afterthought, PbD emphasizes embedding privacy considerations into the design process.
Key privacy-by-design practices include:
- Conducting privacy impact assessments for new technologies and projects to assess their potential risks and implement appropriate mitigation strategies.
- Adopting privacy-enhancing technologies such as differential privacy, federated learning, and homomorphic encryption to protect data privacy while enabling analytics and insights.
- Being transparent about data collection, use, and sharing practices, obtaining informed consent from individuals before processing their data, and providing clear opt-out mechanisms.
Remember, data protection is not a one-time effort. Continuously assess your security posture, update technologies and practices, and conduct regular vulnerability assessments and penetration testing to foster a culture of data security awareness within your organization and educate employees about data protection policies, best practices, and the importance of compliance.
Conduct regular internal data audits.
Ensuring data compliance starts with understanding the data your business collects, analyzes, and stores and what they're used for. One way to do that is through regular internal data audit — a comprehensive review and analysis of your existing data policies, practices, and assets. It's also a systematic evaluation process to ensure data management aligns with the relevant compliance and regulatory requirements.
Internal data audits are important for a few reasons:
- Ensure regulatory compliance: Internal audits systematically assess your data handling practices against relevant regulations to identify areas where your processes, procedures, or controls might not be compliant, highlighting potential weaknesses before external or regulatory audits.
- Mitigate compliance risks: Digital transformation involves gathering and processing new data types, leading to potential regulatory compliance gaps. A data audit identifies these gaps and helps you implement compliance controls.
- Build trust and transparency: Internal audits also showcase your commitment to data privacy and security, enhancing your reputation. Demonstrating that you handle data responsibly fosters trust with customers and stakeholders.
- Improve data management: Internal data audits involve mapping data flows, identifying redundant data, and streamlining processes, resulting in better data governance, improved data quality, and better-informed business decisions.
Implementing data protection measures and conducting internal data audits contribute to a robust data security posture. Let's discuss how in the next section.
Ensuring compliance in the age of digital transformation
Digital transformation has created immense opportunities for enterprises and exposed them to new data security and privacy risks. So, enterprises adopting emerging tech like cloud computing, IoT, and AI must proactively safeguard data and ensure compliance.
Some best practices are regular internal data audits, robust policies and procedures, reviewing existing compliance programs, implementing layered data protection, and adopting a structured ISMS framework. These allow organizations to map their data, identify and mitigate risks, apply appropriate safeguards tailored to data types and sensitivities, and foster an organization-wide security culture.
With cyber threats constantly advancing, compliance requirements expanding, and data volumes growing, organizations must prioritize data security and privacy and implement best practices while keeping their data safe, compliant, and reliable.
6clicks' regulatory compliance solutions
6clicks' compliance management solution provides a comprehensive and structured approach to managing your organization's policies and compliance obligations.
From our content library, choose from ISO 27001 and other audit and assessment templates, policy and control sets, risk and issue libraries, playbooks and project plans, and more.
In addition, automatically map controls back to your compliance obligations and identify non-compliance areas with Hailey GPT — our AI advanced engine. Identify compliance gaps and control sets against hundreds of frameworks to better manage risk and demonstrate compliance with ease.
Empower your organization to make informed, compliance-centric decisions and foster a culture of trust and accountability with 6clicks.
Experience a demonstration of how our AI-powered platform for cyber risk and compliance can help you.
Empower your organization to make informed, compliance-centric decisions and foster a culture of trust and accountability with 6clicks.
Written by Louis Strauss
Louis began his career in Berlin where he also founded Dobbel Berlin – Berlin’s curated search engine. Returning to Melbourne to join KPMG, Louis lead the development of software designed to distribute IP and create a platform for us by advisors and clients. While at KPMG, Louis also co-authored Chasing Digital: A Playbook for the New Economy. Louis is accomplished in stakeholder management, requirements gathering, product testing, refinement and project implementation. Louis also holds a Bachelor of Engineering and a Masters of Information Systems from the University of Melbourne.








