While NIST CSF and NIST Special Publication 800-53 have some overlap, they serve different purposes and are not subsets of one another. However, these frameworks can be used complementarily, with NIST CSF offering a broader cybersecurity structure and NIST 800-53 providing more specific security control guidance.
What is NIST CSF?
The NIST CSF standards for the National Institute of Standards and Technology Cybersecurity Framework and is a comprehensive set of guidelines, best practices, and standards developed by the US National Institute of Standards and Technology (NIST). Initially designed to bolster the cybersecurity defenses of critical infrastructure, the NIST CSF has since evolved and gained widespread adoption across a diverse range of sectors, proving to be an invaluable tool for organizations seeking to enhance their cybersecurity resilience.
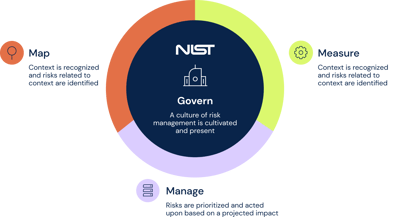
The framework advocates a flexible and customizable approach, enabling organizations to effectively assess, manage, and improve their cybersecurity risk management processes. It encompasses five core functions: Identify, Protect, Detect, Respond, and Recover. Each function plays a crucial role in fostering a robust cybersecurity posture:
- Identify - Develop an organizational understanding of managing cybersecurity risk to systems, assets, data, and capabilities
- Protect - Implement safeguards to ensure the delivery of critical infrastructure services
- Detect - Define the appropriate activities to identify the occurrence of a cybersecurity event
- Respond - Establish appropriate activities to take action regarding a detected cybersecurity event
- Recover - Plan for resilience and to restore any capabilities or services that were impaired due to a cybersecurity event
Through the integration of these functions, organizations are empowered to prioritize their cybersecurity activities, effectively communicate and manage cybersecurity risks, and ultimately strengthen their resilience against cyber threats. The NIST CSF remains a cornerstone in the realm of cybersecurity, guiding organizations in the establishment and refinement of their cybersecurity practices, irrespective of their size or industry.
What is NIST 800-53?
NIST 800-53 is a publication from the National Institute of Standards and Technology (NIST) that provides a set of security controls and guidelines for federal information systems and organizations. These controls cover a range of security measures, including access control, incident response plan, and security frameworks.
While compliance with NIST 800-53 is not mandatory for non-federal organizations, it may be required as part of contracts or agreements with federal agencies. In general, any organization that wants to ensure the security of its information systems can benefit from implementing the controls and guidelines outlined in NIST 800-53.
The publication is intended to help organizations protect their information and information systems from potential threats, such as cyber attacks and data breaches.
What is the difference between NIST CSF and NIST 800-53?
What are the benefits of NIST 800-53?
Some of the benefits of NIST 800-53 include:
- Improved security - The controls and guidelines outlined in NIST 800-53 are designed to help organizations protect their information and information systems from potential threats. By implementing these controls, organizations can reduce their risk of security incidents and improve their overall security posture.
- Compliance with US federal government standards - NIST 800-53 is a publication from NIST, which is a US government federal agency. By implementing the controls and guidelines in NIST 800-53, organizations can ensure that they are compliant with federal security standards.
- Customization - NIST 800-53 includes a detailed set of security controls that can be customized and tailored to the specific needs of an organization. This allows organizations to implement only the controls that are relevant to their particular environment and needs.
- Enhanced protection of sensitive information - Many of the controls and guidelines in NIST 800-53 are specifically designed to protect sensitive or confidential information. By implementing these controls, organizations can ensure that their sensitive information is adequately protected.
What are the NIST 800-53 compliance best practices?
To ensure compliance with NIST 800-53, it is important to follow some best practices. Some of these best practices include:
- Understand the requirements - Before implementing any controls or guidelines from NIST 800-53, it is important to thoroughly understand the requirements and what is expected of your organization. This may involve reading the publication carefully and consulting with security experts or other knowledgeable individuals.
- Customize the controls - NIST 800-53 includes a detailed set of security controls that can be customized and tailored to the specific needs of your organization. Take the time to carefully consider which controls are relevant to your environment and needs, and implement only those that are necessary.
- Create a plan - Before implementing any controls from NIST 800-53, it is important to create a plan that outlines the specific steps that need to be taken to comply with the guidelines. This plan should include timelines, responsibilities, and any other relevant details.
- Monitor and review - Compliance with NIST 800-53 is not a one-time event. It is important to practice continuous monitoring and review your organization's security posture to ensure that the controls and guidelines are being implemented and maintained as intended.
- Seek help - If you are unsure about how to comply with NIST 800-53 or have any other questions, don't hesitate to seek help from security experts or other knowledgeable individuals. There are many resources available to help organizations implement the controls and guidelines outlined in NIST 800-53.
By following these best practices, your organization can ensure that it is compliant with NIST 800-53 and is adequately protecting its information and information systems from potential threats. Improve your cybersecurity posture by implementing NIST CSF 800-53 controls with 6clicks. The 6clicks platform helps automate and demonstrate NIST CSF compliance, thereby helping you protect your systems from evolving threats.
Explore our solution for NIST including 800-53 and CSF here.
A breakdown of security and access control families in the NIST 800-53 Framework
The NIST 800-53 framework provides a comprehensive set of security and access controls that organizations can use to protect their information systems and ensure compliance with federal regulations. The framework is organized into 20 security and control families, each addressing specific aspects of security.
The breakdown of security and access control families in the NIST 800-53 Framework covers a wide range of areas, including access control, audit and accountability, configuration management, contingency planning, identification and authentication, incident response, media protection, physical and environmental protection, and system and communications protection, among others.
These families provide a structured approach to addressing security risks and include specific controls to implement and maintain security measures. For example, the access control family includes controls such as account management, access enforcement, and least privilege. The audit and accountability family includes controls for audit generation, audit review, and audit reduction.
The selection of security controls is guided by the impact levels defined by Federal Information Processing Standards (FIPS) Publication 199. The impact levels (low, moderate, and high) reflect the potential impact that a breach or compromise of the information would have on the organization. The impact level determines the minimum set of security controls that must be implemented to protect the information system adequately.
By following the NIST 800-53 framework and selecting the appropriate security controls from the relevant control families, organizations can establish a strong security posture and mitigate risks to their information systems. Tools like 6clicks can help streamline the compliance process by providing a centralized platform for managing compliance efforts and automating control assessments.
NIST 800-53 can be used by any organization
NIST Special Publication 800-53 provides a comprehensive set of security and privacy controls for information systems and organizations. While it was originally developed for federal government agencies, its flexible framework can be applied by any organization seeking to enhance their cybersecurity posture and comply with industry standards. NIST 800-53 offers a catalog of controls organized into families, allowing organizations to select and implement the controls that are most relevant to their specific needs and requirements. It covers a wide range of areas, including insider threats, supply chain risk management, risk assessment, and cyber risk.
By adopting and implementing the controls outlined in NIST 800-53, organizations can establish a robust risk management strategy, strengthen their security programs, and protect their critical assets and information from hostile attacks and human error. One tool that organizations can leverage to streamline their NIST 800-53 compliance efforts is 6clicks, an integrated risk and compliance platform that provides a consolidated control catalog, automated risk assessment, and management through control compliance. With the guidance of NIST 800-53 and the support of solutions like 6clicks, organizations can navigate the complex cybersecurity landscape and safeguard their operations and sensitive data.
What you should do now
Now that you have a better understanding of NIST Special Publication 800-53 and its significance in enhancing cybersecurity and compliance, it's time to consider what steps you should take next to ensure NIST 800-53 compliance for your organization.
Given the complexity and breadth of the controls outlined in NIST 800-53, it is advisable to assemble a team of experts who possess a deep understanding of the framework and its requirements. This team can take the lead in guiding your organization through the compliance process, ensuring that all necessary controls are implemented effectively.
In addition to assembling an expert team, it is beneficial to leverage automated security platforms, such as 6clicks, to streamline your compliance journey. 6clicks offers a comprehensive and integrated risk and compliance solution, specifically designed to support organizations in achieving NIST 800-53 compliance. This platform provides features like a consolidated control catalog and automated risk assessment, simplifying the process of selecting and implementing the relevant controls.
By utilizing 6clicks or similar automated security platforms, your organization can save time and effort in manually managing compliance processes. This allows you to focus on strengthening your cybersecurity posture and ensuring the protection of your critical assets and sensitive information.
How to ensure you're NIST SP 800-53 compliant
Ensuring compliance with NIST Special Publication (SP) 800-53 is essential for federal government agencies, as well as private organizations that handle governemtn information. This framework provides a comprehensive set of security and privacy controls for information systems and organizations, with the aim of protecting national security, critical infrastructure, and safeguarding against insider threats, hostile attacks, and human error. To ensure compliance with NIST SP 800-53, it is recommended to assemble a team of experts well-versed in the framework's requirements. Additionally, leveraging automated security platforms like 6clicks can streamline the compliance journey by providing a consolidated control catalog and automated risk assessments, ultimately saving time and effort in managing compliance processes. By prioritizing NIST SP 800-53 compliance, organizations can enhance their cybersecurity posture and effectively protect their valuable assets and sensitive information.
Delegate responsibility
When it comes to NIST SP 800-53 compliance, delegate responsibility plays a critical role in ensuring that federal agencies and organizations meet the necessary security requirements. It is essential to designate a dedicated individual or team to assess, implement, and monitor the selected controls.
Delegate responsibility is crucial as it allows for better coordination and accountability throughout the compliance process. By assigning specific roles and responsibilities, organizations can streamline their compliance efforts and avoid confusion or duplication of efforts. This approach ensures that all necessary security controls are properly implemented and continuously monitored.
Continuous adherence monitoring is a key aspect of NIST SP 800-53 compliance. It is important to have mechanisms in place to consistently track and evaluate compliance with the selected controls. This allows organizations to identify and address any potential non-compliance issues promptly.
Efficient evidence of compliance is another critical factor to consider. Organizations must be able to provide auditors with the necessary evidence to demonstrate their compliance with NIST SP 800-53 controls. This evidence should be properly documented and easily accessible to facilitate the auditing process.
Understand your existing policies and operation
Understanding your existing policies and operations is essential when striving for NIST 800-53 compliance. Each organization has its own unique set of policies, procedures, and operational needs, which must be taken into consideration when implementing security controls.
By thoroughly understanding your existing policies, you can identify any gaps or areas that need improvement to align with the requirements outlined in NIST SP 800-53. This allows you to tailor your compliance efforts to meet your organization's specific needs.
Additionally, being well-versed in your operations helps you determine how NIST 800-53 controls will impact your systems and processes. This understanding enables you to prioritize and implement controls that are most relevant and effective for your organization.
Privacy and security are critical components of NIST 800-53 compliance. By understanding your existing policies and operations, you can accurately assess your organization's privacy and security needs. This allows you to identify the appropriate controls that address the specific risks and threats your organization faces.
In summary, understanding your existing policies and operations is vital for successful NIST 800-53 compliance. It allows you to tailor controls to meet your organization's specific privacy and security needs, ensuring that you implement the most appropriate and effective measures to protect your systems and data.
Take a common approach to implementation where possible
When it comes to complying with NIST 800-53, taking a common approach to implementation can save valuable resources and time for organizations. Luckily, there are several controls within the framework that can be effectively implemented centrally and then embedded in different systems or programs.
By implementing controls centrally, organizations can avoid duplicating efforts and streamline their compliance processes. For example, control guidance on user account access can be utilized as a common policy across multiple systems or programs. This not only saves time in developing individual policies for each system but also ensures consistency and reduces the risk of errors or gaps in security measures.
Taking a common approach to implementation also allows organizations to leverage existing resources and expertise. By developing standardized procedures and guidelines, organizations can optimize their compliance efforts and allocate resources more effectively.
By adopting a common approach to implementation where possible, organizations can achieve NIST 800-53 compliance more efficiently and effectively. This not only saves time and resources but also ensures a consistent and robust security posture across the organization.
Reference the control catalog
When it comes to NIST 800-53 compliance, referencing the control catalog is of utmost importance. The control catalog serves as a comprehensive resource that provides valuable information and guidance for organizations to effectively implement and adapt controls based on their specific requirements or risk profiles.
By referencing the control catalog, organizations gain access to a robust set of controls that are designed to address a wide range of security and privacy risks. This catalog includes control families that cover various aspects of information security, such as access control, incident response, and system and information integrity.
One of the key benefits of using the control catalog is that it helps organizations identify the interdependencies between controls. Some controls may rely on or be connected to others, and understanding these relationships is crucial for a successful implementation. The control catalog offers clear guidance on which controls are related, allowing organizations to take a systematic approach to implementation.
Moreover, referencing the control catalog enables organizations to customize their control selection process based on their unique requirements. It provides additional information on control enhancements and control baselines, allowing organizations to choose the most appropriate controls for their specific security needs and risk appetite.
Record evidence of implementation
Recording evidence of implementation for NIST SP 800-53 controls is of utmost importance for organizations seeking compliance with the framework. This documentation serves as proof that the necessary security controls have been implemented and are functioning effectively.
To demonstrate compliance with each individual control, organizations must maintain records that clearly show how the control is implemented, managed, and monitored. This includes documenting the specific actions taken to implement the control, as well as any changes made over time. These records provide a comprehensive overview of the organization's efforts to address security risks and meet the requirements of the control.
Furthermore, documentation and records are invaluable in demonstrating overall compliance with the NIST SP 800-53 framework. By maintaining a record of the implementation status and effectiveness of each control, organizations can easily demonstrate their adherence to the framework's requirements. These records also facilitate regular audits and assessments, providing assurance to stakeholders that the organization is following best practices and maintaining a strong security posture.
Proper record-keeping offers several benefits. It allows organizations to track and manage their progress in implementing security controls, enabling them to identify any gaps or weaknesses that need to be addressed. It also ensures that critical information is accessible for future reference, including during incident response or when conducting risk assessments. Furthermore, having well-documented records supports knowledge transfer within the organization and enables effective communication with auditors and regulators.
6clicks and NIST standards
6clicks streamlines the adoption of NIST standards by providing pre-configured content specifically for NIST CSF and SP 800-53, simplifying asset identification, and enhancing risk management. 6clicks fosters a collaborative approach by enabling task assignments across teams, ensuring comprehensive involvement in security efforts. It further bolsters compliance confidence through rigorous internal and supplier audits, utilizing its Hailey AI technology to cross-reference compliance frameworks efficiently.
If you'd like to learn more, book a demo below.
Written by Andrew Robinson
Andrew started his career in the startup world and went on to perform in cyber and information security advisory roles for the Australian Federal Government and several Victorian Government entities. Andrew has a Masters in Policing, Intelligence and Counter-Terrorism (PICT) specialising in Cyber Security and holds IRAP, ISO 27001 LA, CISSP, CISM and SCF certifications.