Definition of ISMS risk register
A risk register is an integral part of an organization's Information Security Management System (ISMS). It is a valuable tool that helps identify, assess, and manage risks to the organization's information assets and infrastructure. The risk register documents potential risks, their potential impact, and the risk treatment plan. It helps in the risk management process by identifying risk owners and assigning responsibility for managing specific risks. The risk register also tracks the residual risk after implementing control measures and provides a comprehensive view of the organization's risk landscape. By conducting regular risk assessments and evaluating the effectiveness of risk treatment options, organizations can effectively manage security risks, including those related to mobile devices, loss of confidentiality, and security incidents. The risk register guides security teams, project managers, and other stakeholders in developing action plans and security management strategies to mitigate risks and ensure the organization operates within an acceptable level of risk. To ensure compliance with regulations and industry standards, organizations need to maintain an up-to-date risk register and integrate it into their overall risk management methodology and plan.
Purpose of an ISMS risk register
The purpose of an ISMS (Information Security Management System) risk register is to effectively identify, assess, and prioritize risks within an organization. It plays a crucial role in helping stakeholders understand and manage potential risks, ensuring the security of sensitive information.
The ISMS risk register serves as a central repository where all potential risks are recorded and monitored. It allows organizations to proactively identify and analyze threats, vulnerabilities, and potential impacts to their information security. By documenting these risks, organizations can better understand the likelihood and impact of each risk, making informed decisions regarding risk treatment strategies.
One of the key benefits of the ISMS risk register is its ability to prioritize risks. By assigning a risk rating or level of significance to each identified risk, organizations can focus their resources and efforts on addressing the most critical threats first. This ensures that limited resources are effectively allocated to manage risks in a way that aligns with the organization's risk appetite.
Furthermore, the ISMS risk register facilitates the development of a comprehensive risk treatment plan. It helps organizations evaluate various risk treatment options and select the most suitable strategies to mitigate or control identified risks. This allows organizations to establish appropriate controls, implement security measures, and develop action plans to address potential security incidents.
Components of an ISMS risk register
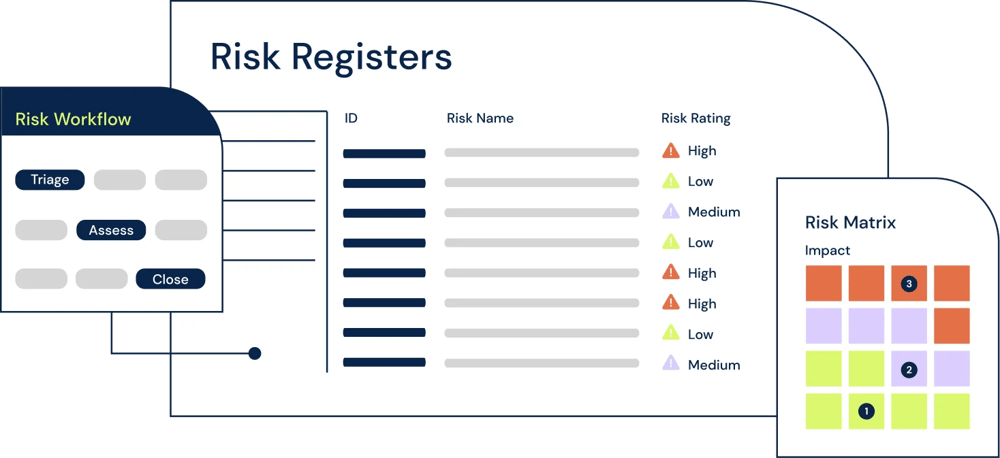
The ISMS risk register is a crucial component of an organization's risk management process. It serves as a centralized tool to record and monitor all potential risks to information security. This article will explore the key components of an ISMS risk register and highlight its significance in the risk management methodology. From risk identification to risk treatment and evaluation, the ISMS risk register helps organizations proactively address risks and protect their valuable assets. By understanding the components and functionalities of an ISMS risk register, organizations can effectively prioritize risks and develop appropriate strategies to mitigate them.
Potential risks and impacts
Potential risks and impacts are crucial considerations in the ISMS risk register. By analyzing the identified threats and vulnerabilities for each asset, organizations can better understand and mitigate potential risks to their information security.
Using a scale from 1-10, the likelihood of each risk occurring and the impact it would have on the business can be assessed. This helps prioritize risks, focusing resources on those with higher potential for significant consequences.
While monetary impacts such as financial loss are important, it is equally important to consider non-monetary impacts. These include potential damage to brand reputation, strained customer relationships, legal or contractual issues, and compliance failures.
For example, a security incident resulting in a breach of customer data can significantly tarnish a company's reputation and erode trust. This may lead to customer churn, loss of business opportunities, and regulatory penalties. These non-monetary impacts can have long-lasting effects that go beyond immediate financial losses.
By including non-monetary impacts in the risk assessment process, organizations gain a more comprehensive understanding of the potential risks they face. This holistic approach enables them to make informed decisions about risk treatment options, prioritize actions, and allocate resources effectively to safeguard the business against both monetary and non-monetary consequences.
Acceptable level of risk
In the ISMS risk register, determining and defining the acceptable level of risk is a crucial step in the risk management process. The acceptable level of risk refers to the level of risk that an organization is willing to tolerate in pursuit of its objectives. It is essential to strike a balance between potential rewards and potential losses when setting the acceptable level of risk.
When determining the acceptable level of risk, organizations need to consider both the potential gains from taking on the risk and the potential impact or losses it may have on the organization. This means evaluating the potential benefits or rewards that may arise from the risk, such as increased profitability, market share, or competitive advantage. Simultaneously, it is equally important to assess the potential organizational impact if the risk materializes, which could include reputational damage, financial loss, legal implications, customer dissatisfaction, or regulatory non-compliance.
Several factors should be taken into consideration when determining the acceptable level of risk within the ISMS risk register. These factors may include the organization's risk appetite, strategic objectives, legal and regulatory requirements, industry standards, stakeholder expectations, and the potential for harm to individuals or the broader society.
By considering these factors and weighing the potential rewards against the potential losses, organizations can set an acceptable level of risk that aligns with their overall risk management strategy and objectives. This ensures that risks are assessed and treated in a manner that is in line with the organization's risk appetite and tolerance, allowing them to make informed decisions about the risks they are willing to accept within their ISMS.
Risk owners and security teams
Risk owners and security teams play crucial roles in managing and mitigating risks within an ISMS risk register.
Risk owners are individuals or departments within an organization who are responsible for managing specific identified risks. They have a deep understanding of the risks associated with their area of expertise and are accountable for implementing risk treatment plans to address those risks. Risk owners are responsible for coordinating and collaborating with relevant stakeholders to ensure the effective management of risks. They regularly monitor and evaluate the status of risks, identify potential risk treatment options, and make informed decisions regarding risk acceptance or mitigation.
Security teams, on the other hand, are responsible for ensuring the overall security of the organization. In the context of the ISMS risk register, security teams are heavily involved in conducting risk assessments. They identify and analyze potential risks, assess their likelihood and potential impact, and assign risk ratings. Based on these assessments, security teams collaborate with risk owners to develop and implement appropriate risk treatment plans. This may involve implementing security controls, such as firewalls, encryption, access controls, and monitoring systems, to mitigate the identified risks.
Overall, risk owners and security teams work together closely within the ISMS risk register. While risk owners manage and coordinate the treatment of identified risks, security teams provide the necessary expertise and support in conducting risk assessments and implementing security controls to safeguard the organization against potential threats. Their collaboration ensures a comprehensive approach to risk management and the protection of organizational assets and information.
Action plans for treatment of risks
Action plans for the treatment of risks are crucial for organizations to effectively mitigate and manage unacceptable risks identified in the risk assessment process. These action plans outline specific steps and strategies to address and reduce the likelihood and impact of identified risks.
The Risk Treatment Plan serves as the implementation roadmap for these action plans. It provides a structured approach to addressing risks, assigning responsibilities to individuals or departments, defining timelines for completion, and allocating budgets for each control measure.
The four options available for handling unacceptable risks in ISO 27001 are risk avoidance, risk transfer, risk mitigation, and risk acceptance. Risk avoidance involves eliminating or avoiding the risk altogether by discontinuing activities that pose the risk. Risk transfer involves transferring the risk to a third party, such as through insurance or outsourcing. Risk mitigation involves implementing control measures to reduce the likelihood and impact of the risk. Risk acceptance involves consciously deciding to tolerate the risk, either because the cost of mitigation outweighs the potential impact or because the risk falls within an organization's risk appetite.
Moving from theoretical risk management to practical implementation is crucial to achieve effective information security. It requires organizations to not only identify and assess risks but also take the necessary actions to mitigate and manage them. By following the action plans outlined in the Risk Treatment Plan, organizations can ensure that control measures are implemented, responsibilities are assigned, and risks are effectively managed in order to protect their information assets and achieve their information security objectives.
How to create an ISMS risk register
Creating an Information Security Management System (ISMS) risk register is a crucial step in effectively managing and mitigating potential risks to an organization's information assets. The ISMS risk register serves as a central repository for documenting and analyzing risks, ensuring that they are understood and properly addressed throughout the organization. By implementing a comprehensive risk register, organizations can identify and prioritize risks, assign ownership to their management, and develop appropriate measures to minimize their potential impact. In this article, we will discuss the key steps involved in creating an ISMS risk register, including risk identification, assessment, treatment, and ongoing monitoring.
Explore how to automate your ISMS in 6clicks here.
Establish a process for assessing risks
Establishing a process for assessing risks is a crucial component of an Information Security Management System (ISMS) risk register. This process involves identifying and evaluating potential risks to the organization's assets, evaluating the probability and potential impact of these risks, and determining appropriate risk treatment plans.
The process begins by listing the assets, threats, and vulnerabilities in separate columns within the risk register. Each risk is assigned a unique risk ID and a designated risk owner for accountability. Additionally, each risk is assessed based on its potential impact and likelihood of occurring.
Risk evaluation involves comparing each assessed risk against predetermined levels of acceptable risk. By doing so, organizations can prioritize which risks require immediate attention and which can be addressed at a later stage. Those risks that exceed the predetermined acceptable level may warrant immediate action, while those falling within an acceptable range may be monitored or addressed through alternative risk treatment options.
The process of assessing risks in an ISMS risk register is dynamic and iterative, necessitating regular updates and reviews. As new threats emerge and the risk landscape evolves, organizations need to reassess their risk register to ensure timely and effective risk management. By establishing a robust and systematic process for risk assessment, organizations can identify and mitigate potential threats, ultimately enhancing the security and resilience of their information systems and assets.
Written by Andrew Robinson
Andrew started his career in the startup world and went on to perform in cyber and information security advisory roles for the Australian Federal Government and several Victorian Government entities. Andrew has a Masters in Policing, Intelligence and Counter-Terrorism (PICT) specialising in Cyber Security and holds IRAP, ISO 27001 LA, CISSP, CISM and SCF certifications.






.webp?width=1000&height=637&name=Risk-management-feature-identify-manage-and-treat-risks%20(2).webp)