Key takeaways
- ISO 27002:2022 is an updated version of the international management standard for information security controls, providing detailed guidance on implementing specific controls within an information security management system (ISMS).
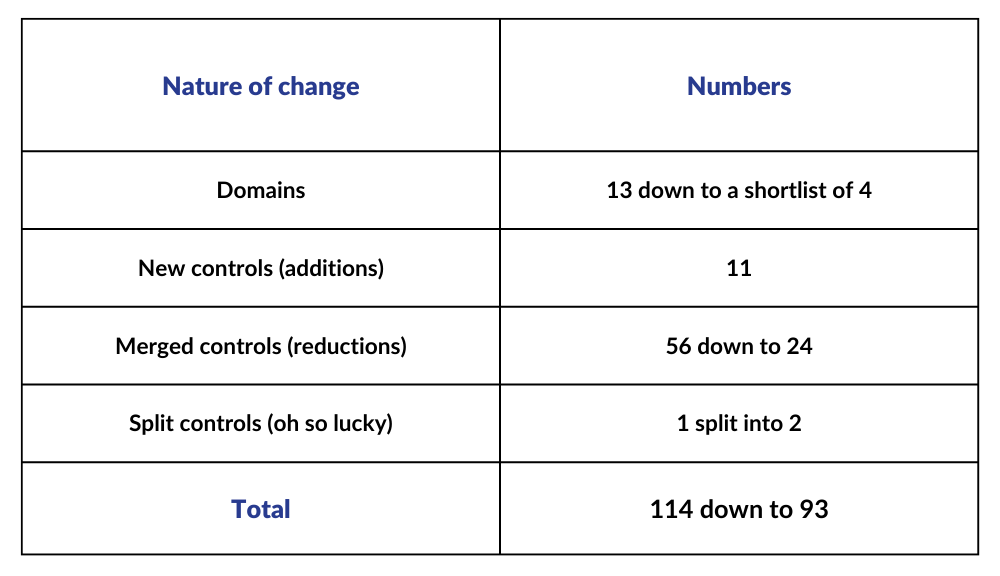
- The update introduces new controls addressing emerging risks and technological advancements while streamlining and condensing existing controls for improved usability.
- Compliance with ISO 27002 involves establishing an information security policy, conducting risk assessments, implementing controls, and maintaining incident response and business continuity plans.
In the world of international management standards, change is the only constant. ISO 27001 and ISO 27002, originally published in 2005 with updates in 2013, have now received significant updates in 2022. In this article, we will delve into the changes introduced in ISO 27002:2022 specifically, including control additions, reasons behind those additions, and reductions or merged controls.
ISO 27001 vs. ISO 27002: The difference
Within the realm of global information security management standards, ISO 27001 and ISO 27002 fulfil unique yet interrelated functions. While ISO 27001 sets the comprehensive framework for establishing, implementing, maintaining, and continuously improving an information security management system (ISMS), ISO 27002 provides detailed guidance on selecting and implementing specific controls within the ISMS. ISO 27001 emphasizes the importance of conducting risk assessments and adopting a risk management approach to protect information assets and manage security risks effectively.
On the other hand, ISO 27002 offers detailed guidance on how to implement Annex A of ISO 27001, which consists of the list of security controls set out in the standard. This supplementary guidance delves further into technical issues such as authentication mechanisms, access rights, and encryption practices that organizations need to consider when creating their cyber and information security strategies. Understanding the key differences between ISO 27001 and ISO 27002 is crucial for organizations aiming to achieve comprehensive and effective information security management.
ISO 27001: A steady ship in a fast-changing environment
In the fast-paced industry of cyber and information security, ISO 27001 remains a reliable and steady ship amidst rapid changes. It provides organizations with a solid foundation for establishing and maintaining an ISMS based on a risk management approach. By incorporating risk assessment methodologies and a continual improvement cycle, ISO 27001 enables organizations to adapt to the evolving threat landscape and meet the challenges of a dynamic information security environment. It serves as a robust management standard that helps organizations establish and demonstrate their commitment to information security.
A closer look at ISO 27001 Annex A and ISO 27002
ISO/IEC 27002:2022, also known as ISO 27002, serves as a comprehensive resource offering valuable insights and recommendations regarding the careful selection, seamless implementation, and efficient management of security controls tailored to an organization's unique information security risk landscape. It provides supplementary guidance that supports ISO 27001 and offers more detailed information on the specific controls organizations can apply from ISO 27001 Annex A.
The older version of ISO 27002 organizes the controls into 14 main groups:
- A.5 Information security policies
- A.6 Organization of information security
- A.7 Human resource security
- A.8 Asset management
- A.9 Access control
- A.10 Cryptography
- A.11 Physical and environmental security
- A.12 Operations security
- A.13 Communications security
- A.14 System acquisition, development, and maintenance
- A.15 Supplier relationships
- A.16 Information security incident management
- A.17 Information security aspects of business continuity management
- A.18 Compliance
These groups covered various aspects of information security, providing organizations with guidance on developing and implementing effective controls. By following the guidance of ISO 27002, organizations can enhance their information security practices and ensure compliance with industry best practices.
The 2022 version of ISO 27002 organizes the controls into just 4 main groups (but read on to find out about the new attributes):
- 5 Organizational controls
- 6 People controls
- 7 Physical controls
- 8 Technological controls
ISO 27002 is designed to be used by organizations that intend to:
- Select controls within the process of implementing an Information Security Management System (ISMS) based on ISO/IEC 27001.
- Implement commonly accepted information security controls.
- Develop their own information security management guidelines.
By utilizing ISO 27002, organizations can establish a robust framework for information security management, align their practices with international standards, and effectively mitigate risks to their information assets.
ISO 27001 Annex A and 27002:2022 introduces new control attributes
One notable change in ISO 27002:2022 is the introduction of control attributes. These attributes include control type, information security properties, cybersecurity concepts, operational capabilities, and security domains. The inclusion of control attributes enhances the risk treatment planner or security architect's ability to develop a diverse control environment, avoiding overreliance on specific control types. This emphasis on control attributes facilitates a more comprehensive risk assessment and allows organizations to tailor their security controls to their specific needs and objectives, and ensure comprehensive coverage.
New controls introduced in 2022
ISO/IEC 27002:2022 incorporates new controls reflecting key trends and drivers in the industry. These controls address emerging risks and technological advancements. They include areas such as threat intelligence, information security for cloud services, ICT readiness for business continuity, physical security monitoring, configuration management, information deletion, data masking, data leakage prevention, monitoring activities, web filtering, secure coding, and more. By incorporating these new controls, organizations can enhance their security management practices and address the evolving challenges of the digital landscape.
Key drivers behind the new controls
The new controls in ISO/IEC 27002:2022 align with key drivers shaping the industry. Cloud controls respond to the rise of cloud computing, the dominance of global cloud service providers, service vulnerabilities, and concerns related to data sovereignty. Business continuity planning gains renewed importance due to the impact of events such as the COVID-19 pandemic, ransomware attacks, and natural disasters. Mobility controls accommodate the growing trend of remote work and the need to secure mobile devices. Secure code and privacy controls address vulnerabilities and the increasing significance of privacy legislation. Lastly, visibility controls foster collaboration between government and industry to combat emerging threats effectively.
Merged controls in ISO/IEC 27001:2022 Annex A and ISO/IEC 27002:2022
ISO/IEC 27002:2022 streamlines the control set by merging controls from the previous version, reducing duplicative controls and enhancing clarity. Out of the 56 merged controls, 24 condensed controls were created in the new version. This consolidation optimizes the control environment without overwhelming organizations. For example, electronic media security controls were merged to reflect the preference for cloud storage, and logging controls were condensed while maintaining visibility. These changes streamline the implementation process and improve the usability of the standard.
Split controls in ISO/IEC 27001:2022 Annex A and ISO/IEC 27002:2022
In ISO/IEC 27002:2022, only one control, Technical Compliance Review, was split into two controls to align with Management of Technical Vulnerabilities and Compliance with Security Policies and Standards. This split reflects the evolving landscape of security management and the need for more focused controls to address specific aspects of compliance and vulnerability management. The integration of these split controls with the merged controls provides organizations with a more comprehensive and tailored approach to information security.
Certification process and internal audit
To achieve certification in ISO 27001, organizations must undergo a certification process conducted by accredited certification bodies. This process typically includes a comprehensive audit of the organization's ISMS against the requirements of ISO 27001 and ISO 27002. The audit evaluates the implementation and effectiveness of the ISMS, ensuring that it aligns with the international standards and meets the organization's information security objectives.
Internal audits play a crucial role in the certification process. Organizations must conduct internal audits to assess the compliance of their ISMS with ISO 27001 and ISO 27002 and identify areas for improvement. Internal audits provide an opportunity for organizations to evaluate their security measures, review the effectiveness of controls based on ISO 27002 guidelines, and identify any non-conformities or gaps in their information security practices. Through regular internal audits, organizations can ensure continuous improvement and maintain their compliance with the international standards.
Summary of compliance requirements
ISO 27001 and ISO 27002 specify a set of compliance requirements that organizations must meet to achieve certification. These requirements include:
-
Establishing an information security policy: Organizations must define and document their information security policy, which should align with their overall business objectives and risk management strategy, as outlined in ISO 27002.
-
Conducting risk assessments: Organizations must conduct risk assessments in accordance with ISO 27002 guidelines. This involves identifying and assessing the risks to their information assets, considering the potential impact and likelihood of risks occurring. Based on the risk assessment, appropriate security controls should be selected and implemented following the recommendations of ISO 27002.
-
Implementing controls: Organizations need to implement a set of controls based on ISO 27002 guidelines to mitigate identified risks and ensure the confidentiality, integrity, and availability of information assets. These controls should cover a wide range of areas, including access control, network security, physical security, encryption, incident response, and more.
-
Managing incidents: Organizations must establish an incident management process following the guidelines provided in ISO 27002. This process includes reporting, investigating, and resolving security incidents in a timely manner.
-
Continual improvement: Organizations should establish a cycle of continual improvement for their ISMS, as recommended by ISO 27001 and ISO 27002. This involves monitoring and reviewing the performance of the ISMS, conducting regular internal audits based on ISO 27002, and taking corrective actions to address any identified non-conformities or areas for improvement.
Summary of security measures
ISO 27002 provides detailed guidance on various security measures that organizations should consider implementing to protect their information assets and manage security risks effectively. These security measures include, but are not limited to:
-
Access controls: Implementing mechanisms to control access to information assets based on user roles and privileges, as specified in ISO 27002. This includes authentication mechanisms, access rights management, and user provisioning processes.
-
Physical security: Implementing measures to secure physical access to facilities, data centers, and critical infrastructure, as outlined in ISO 27002. This can involve physical barriers, surveillance systems, and access control systems.
-
Network security: Implementing firewalls, intrusion detection and prevention systems, and secure network configurations following ISO 27002 guidelines to protect the organization's network infrastructure from unauthorized access and external threats.
-
Encryption: Implementing encryption mechanisms to protect sensitive data both at rest and in transit, as recommended by ISO 27002. This includes encryption of stored data, secure communication protocols, and secure key management practices.
-
Incident response and business continuity: Establishing incident response plans and business continuity plans based on ISO 27002 guidelines to ensure the organization can effectively respond to and recover from security incidents and disruptive events.
By implementing these security measures and complying with the requirements of ISO 27001 and ISO 27002, organizations can enhance their information security posture, meet international standards, and demonstrate their commitment to protecting valuable information assets.
Discover ISO 27001 and ISO 27002
At 6clicks, we're committed to helping you stay updated with the latest changes in international management standards. Our experts are well-versed in ISO 27002:2022 and can guide you through its domains, controls, risk assessment methodologies, and practical implementation. Join us on a journey to explore the updated standard and leverage its strengths for your organization.
With ISO 27002:2022, you can enhance your information security practices, address emerging threats, and ensure compliance with industry best practices. Stay ahead of the curve and make informed decisions by understanding the nuances of ISO 27002:2022.
Don't miss out on the opportunity to optimize your control environment, improve risk management, and strengthen your organization's security posture. Click the button below to embark on an insightful tour with our knowledgeable 6clicks maestros.
Written by Andrew Robinson
Andrew started his career in the startup world and went on to perform in cyber and information security advisory roles for the Australian Federal Government and several Victorian Government entities. Andrew has a Masters in Policing, Intelligence and Counter-Terrorism (PICT) specialising in Cyber Security and holds IRAP, ISO 27001 LA, CISSP, CISM and SCF certifications.